How to Build a Poor Man's Mono/Okra Banking API
Reverse engineer your mobile banking app and make a script that automates checking balances.
I built this out of the curiosity (which won’t kill this cat) I had to see if I could create a Python-based script that automates checking account balances using bank APIs that arent publicly available ala what Plaid, Mono, and Okra do but for free.
Reverse engineering the mobile banking app for my bank was not so hard. The process, however, proved to be very useful and you can easily adapt what I showcase here to your own ideas.
REQUIREMENTS
Download and install Burpsuite, Python, and requests in a virtual environment.
Now let’s get hacking
First, you'll need to know the IP address of your proxy server. On Linux/Mac type "ifconfig" in a terminal to display it. It will probably be something like "192.168.X.X" or "10.X.X.X.".
Configure your mobile device to use the IP address gotten in step (1) as the proxy hostname and use port “8080” as the proxy port.
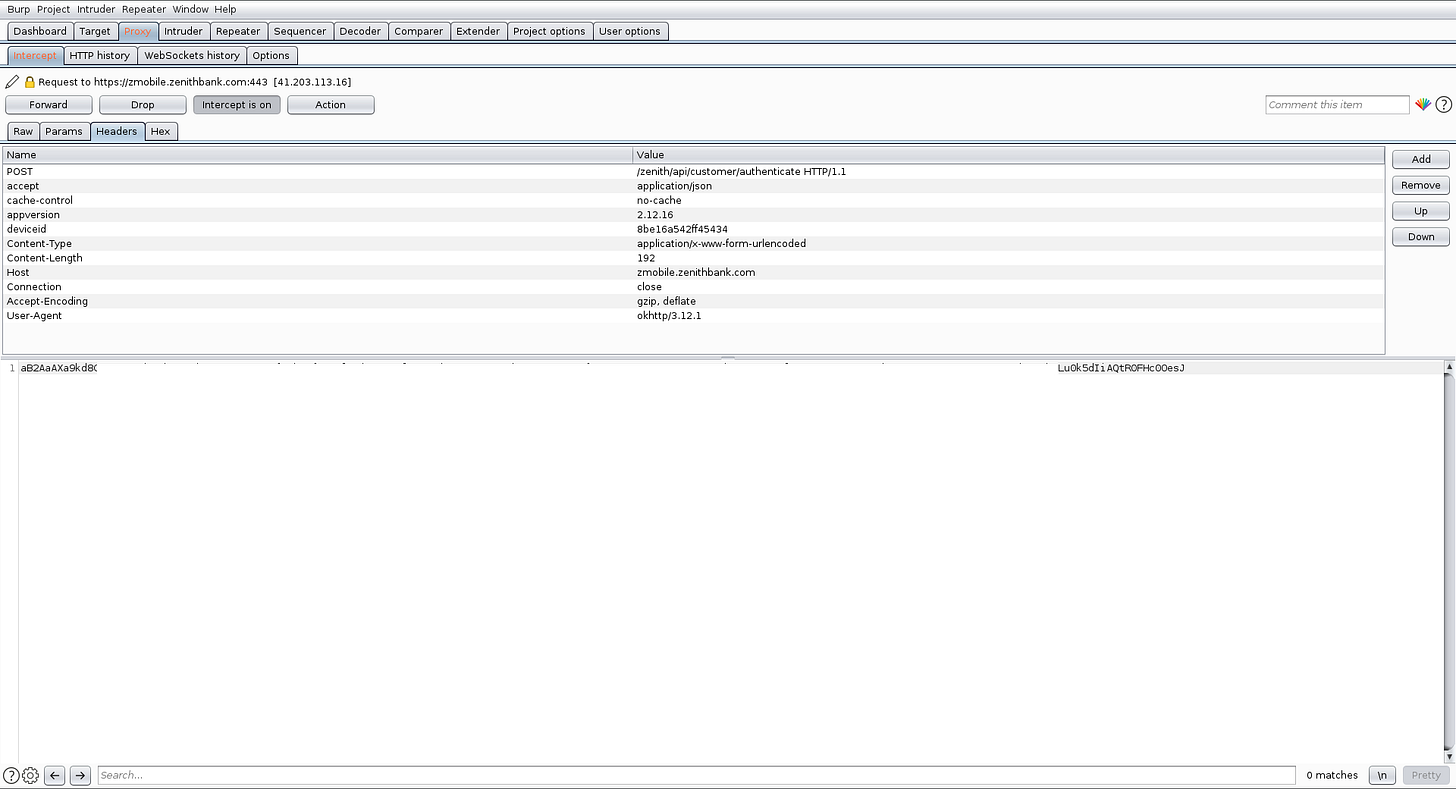
We will use Burp to create a local proxy server that we'll connect our phone to and then use it to read all traffic MITM-style. We will then check the logs in the intercept tab of Burpsuite to find out the called API endpoints and reverse engineer it using Python.
Start Burpsuite with default settings, go to the Proxy tab, click on the sub-tab "options" and edit the "Proxy Listener" to listen on all interfaces. This will ensure that Burpsuite will listen to all traffic to and from your mobile device.
Visit http://burp/cert with your mobile device. A certificate will be automatically downloaded automatically which you will need to install. You will also need to rename the certificate file extension to “.cert” in order to install it. Read more
Keep the ‘Proxy’ -> ‘Intercept’ sub-tab of the Burpsuite application open, you will need to keep clicking on the “forward” button as requests go in and out of your mobile device. This is where you will discover the API endpoints being requested by your banking app.
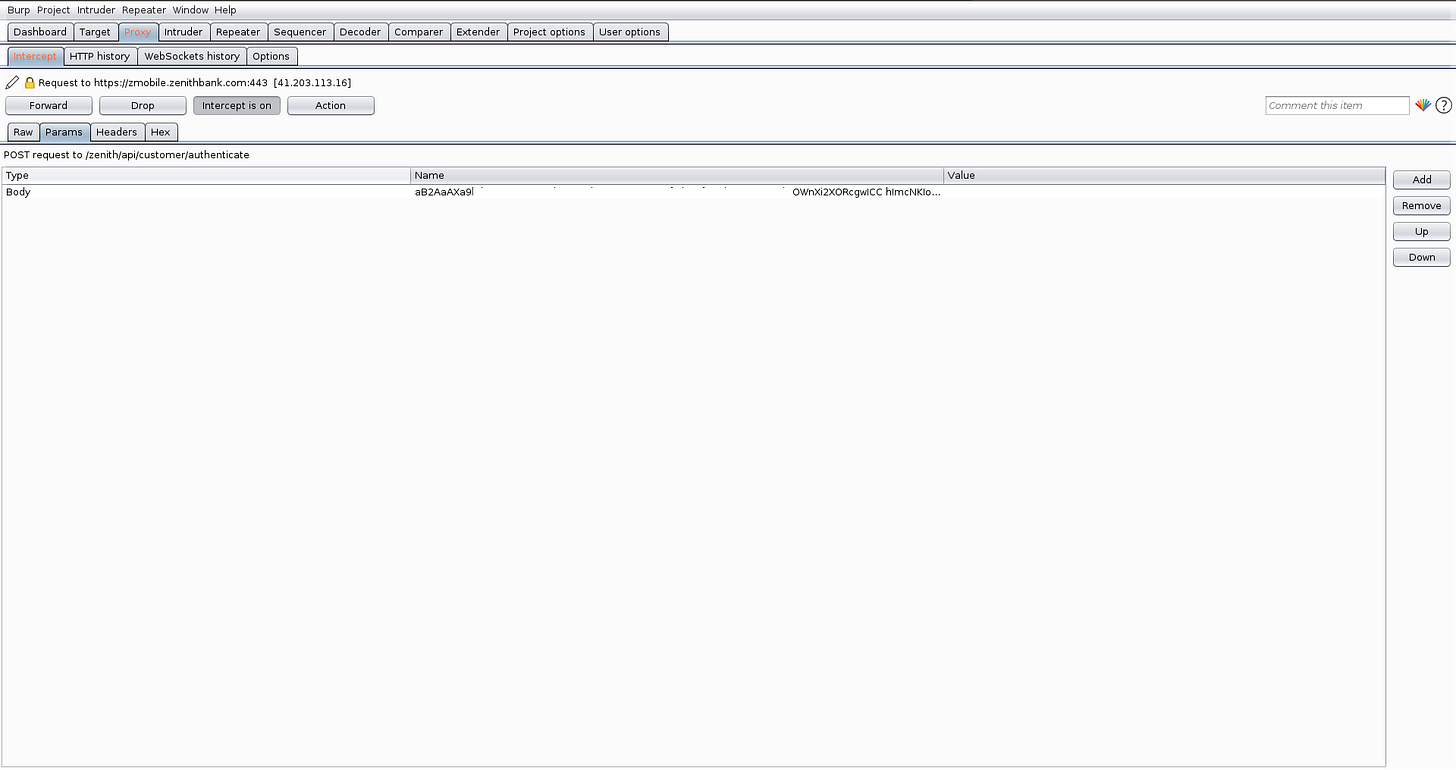
In the images below we discovered the following:
(i) For authentication the mobile app sends a POST request to this endpoint: “https://zmobile.zenithbank.com/zenith/api/customer/authenticate” with a payload.
We will now use Python requests to create a post request and send it to the endpoint we discovered in step (7)
You can see that I have successfully logged in.
In the next part, I will be showing how I fetch my transaction history.


Nice. There are some that encrypt the request body. And even generate a hash for headers.